What is an SQL injection attack?
Cybercrime takes many forms. While many businesses are aware of what and how phishing works, there are other, less well-known attacks that are just as disruptive or damaging.
09.04.21
By Alan Boswell Group

SQL injection attacks are a good example of this – here’s how they work and what you can do to protect your business.
What is an SQL injection attack?
SQL stands for structured query language. Fundamentally, SQL is a language that computers speak to each other in. When you ask a computer to do something, it translates that instruction into an SQL query and then carries out your request.
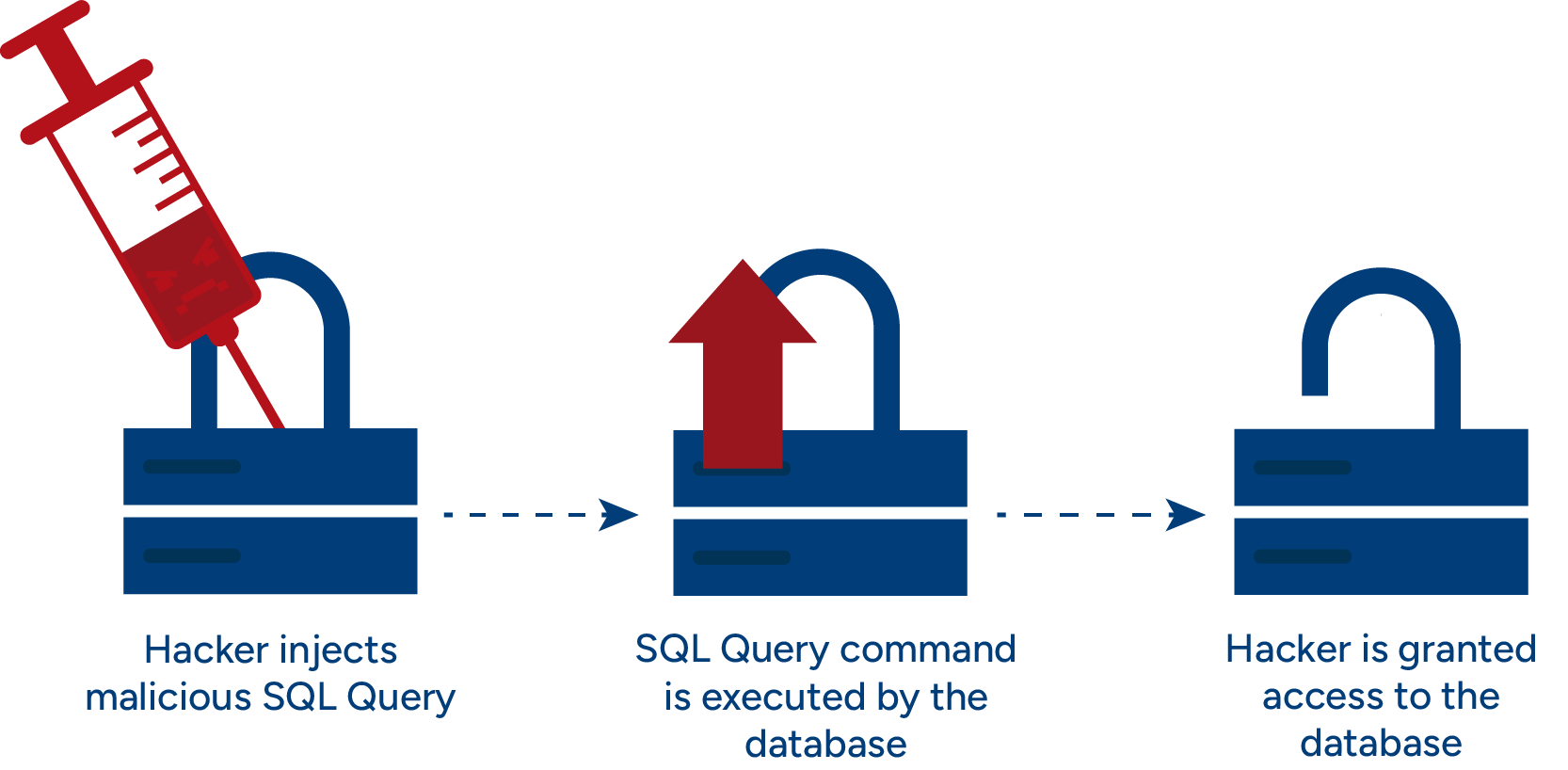
When an SQL injection attack happens, hackers and criminals manipulate that SQL query and gain access to databases stored on your network.
What does an SQL injection attack do?
When criminals get access to your databases, they’re free to manipulate it in any way they want. As well as being able to see all the information you store, they can steal, change and even delete it all.
Criminals can even use an SQL injection attack to design a ‘backdoor’ for themselves that they can use in the future.
Needless to say, the consequences can be devastating especially if databases store information such as names, addresses, bank details or medical records.
What types of SQL injection attack are there?
There are several types of SQL injection attack that hackers choose to use, including:
In-band SQL injection
This is the simplest and easiest type of attack to initiate. It lets criminals launch an attack and get the results they want using the same method. For example, if a criminal knows your username but not your password, they can manipulate the system and gain access using just your username – essentially letting them sign in as you.
Blind SQL injection
With these attacks, hackers don’t have any information to help them access your system. Instead, they have to guess. They’ll do this by asking your system a series of true/false questions from which they can then piece together details about how to gain access.
Blind SQL injection attacks are time consuming as criminals need to ask a whole series of questions to find the answers that will help them access your database.
Error based SQL injection
Similar to Blind SQL injection attacks but instead, criminals ask the system questions that will bring back error messages that (crucially) include details about the database the criminal is trying to access.
Out-of-band SQL injection
This is the opposite of an in-band SQL attack so criminals can’t get the results they want using a single method – this also makes it harder to initiate. Hackers that use out-of-band SQL attacks need the victim’s network to communicate with their own servers and deliver information to them.
How do SQL injection attacks affect businesses?
The consequences of an SQL injection attack can be devastating. Remember – when criminals have access to your databases, they can manipulate them how they please. Potentially, this means stealing the data to sell on the darkweb.
Data manipulation is another possible and hugely disruptive outcome that can affect individuals in a variety of ways. Criminals can also use the attack as a way to extort money from organisations.
SQL injection attacks have been around since 1998 and they show no sign of going away – proof of how effective they are in giving criminals what they want. In fact, data shows that SQL injection attacks make up nearly two thirds of all incidents that occur in web-based applications.
Digital data breaches – such as SQL injection attacks, cost businesses an average of $3.86 million/£2.8 million (including clean-up processes and penalties). In the UK, one of the biggest SQL injection attacks was carried out on TalkTalk who were later fined £400,000 after 150,000 customers had their data stolen.
How to avoid SQL injection attacks
As with all types of cybercrime including DDoS and ransomware attacks, prevention is the best course of action. Basic tips to help minimise the risk of an SQL injection attack include:
Update and patch up any security vulnerabilities (TalkTalk were already aware of issues with security but failed to update their network).
Don’t use what’s called dynamic SQL that allow users to enter live SQL queries, use pre-defined statements instead.
Always use the latest operating system or software. Older versions are more easily compromised (the Panama Papers leak was rumoured to be an SQL attack on databases that were old and poorly maintained).
Encrypt as much sensitive data as possible so it’s harder for criminals to access information.
Cybersecurity firms can also run checks on your system and help you manage your digital security.
It’s also worth taking a look at advice from the National Cyber Security Centre. This is a dedicated platform that helps individuals, as well as small-medium sized businesses and sole traders to keep their digital presence secure.
Does cyber insurance cover SQL injection attacks?
Cyber insurance covers a range of digital threats and can help you investigate a breach, salvage data and cover compensation costs where necessary. Policies can also cover extortion and fraud.
It’s important to bear in mind that cyber insurance varies but whatever you choose, should reflect the nature of your business and take into account the risks you face.
At Alan Boswell Group, we understand that businesses are unique and that one size doesn’t fit all. With that in mind, we’ll always work with you to find a solution that fits your needs.
Need help with your cyber insurance?
Whether you need a quote, have a general enquiry, or want to talk it through over the phone, we're here to help.
Related guides and insights

Data protection insurance – protecting your business from data breach risks
For businesses that fail to protect personal or sensitive data, the financial penalties can be crippling. We look at how data protection insurance can help minimise financial and reputational damage.

Cyber security audits explained
Cyber security audits help identify weaknesses and vulnerabilities, thereby lowering the risk of your business becoming a victim of cybercrime.

Identifying and mitigating cyber security risks in your business
Human error accounts for 95% of all cyber breaches, while more than one in four businesses experienced a cyber security breach in the last 12 months. Here’s how to identify and mitigate cyber security risks for your business.

What is a phishing attack?
As criminals become more sophisticated, scams can be harder to detect and it vital to stay one step ahead.
