What is a Man in the Middle attack?
The government’s latest cyber security breaches survey found that more than one third (39%) of businesses experienced a security breach or attack in the last 12-months.
By Alan Boswell Group

The survey also reveals the average cost to businesses is £8,460, rising to £13,400 for larger firms. But the cost isn’t just financial, it’s time and resources too and while phishing remains the most common type of cyber attack, there are plenty of others that are just as damaging. Here, we explore man in the middle attacks and what you can do to prevent them from happening to you.
What is a man in the middle attack?
As the name suggests, it involves an unwelcome third party. Typically, the ‘man in the middle’ sits in between you and the person or platform you’re trying to communicate with.
The easiest way to think of it, is that the third party is eavesdropping. Their aim is to steal your personal information or manipulate your transaction for their own gain.
How does a man in the middle attack work?
The idea behind a MitM attack is relatively simple so perhaps unsurprisingly, it’s one of the oldest types of cyber attack.
At its simplest form, the third party passively collects your data while they’re in close proximity to you. An example of this type of man in the middle attack would be if someone intercepted your data whilst you were using an unsecured Wi-Fi router in a public place.
In more elaborate schemes, the third party diverts you to a copy of the website you’re trying to visit and is then able to harvest all your information.
What types of MitM attacks are there?
Broadly speaking, man in the middle attacks can take on several guises but fall into one of several key categories, which are:
Eavesdropping
This is a classic example of a man in the middle attack. It involves the criminal tapping into a public Wi-Fi connection that’s unsecured or has poor security. They will then ‘eavesdrop’ on the transactions that are taking place and steal sensitive information such as credit card details.
Spoofing
This involves the man in the middle impersonating a genuine or secure website. By doing this they can get hold of login details, passwords and other sensitive information that can be used for illicit purposes. Some common spoofing techniques include:
IP spoofing – IP stands for internet protocol and it’s how devices identify each other (similar to your postcode). IP spoofing happens when cyber criminals masquerade as someone else by mimicking or faking an IP address which you think is genuine.
DNS spoofing – DNS stands for domain name server which is essentially the name of the website you’re visiting (for example www.abc1.com). With this type of attack, criminals have actually managed to divert you to a fake website which will enable them to steal any personal details you share.
HTTPS spoofing – the ‘S’ stands for secure and means that the website you’re visiting is safe. However, criminals can spoof this and reroute your transaction to an unsecured platform, where (once again) they can gather your data.
Hijacking
This occurs when a criminal takes control over your online transaction such as an email, banking or retail exchange. Common examples of this type of MitM attack are:
Email hijack – this combines an element of spoofing. For example, cyber criminals may monitor communication between a bank and its customers and mimic an email that instructs you to do something to their benefit.
Session hijack – criminals will hijack stored cookies (a data file that contains information specific to your device and usage). Using this information, they can log in as you from their own computer and use your details as if they were you.
How common are MitM attacks?
It’s difficult to estimate how often Man in the Middle attacks occur. Partly, it’s because these types of attacks aren’t discovered until long after the crime has taken place. However, some estimates suggest that around 35% of criminal activity could be considered types of MitM attacks.
How to avoid a man in the middle attack
As with most cyber attacks, prevention is far better than dealing with the consequences and there are several ways you can combat MitM attacks, for example:
Always try to connect to a secure Wi-Fi router, a VPN (virtual private network) can also help although it’s not foolproof.
Use communication platforms that use end to end encryption such as WhatsApp, FaceTime, and Cisco Webex.
Keep your network security updated and patch any vulnerabilities as soon as they’re identified.
Use different passwords for different websites.
Use two factor or multi factor authentication if it’s an option.
How can cyber insurance help?
Cyber crime is one of the biggest risks facing businesses today but while cyber insurance can’t stop security breaches, it can help you manage the effects. It’s also crucial to recognise that cyber attacks aren’t limited to big businesses and wealthy corporations, smaller businesses face the same risks too.
Cyber insurance policies can compensate you for a range of incidents such as data loss, business interruption and reputational damage, as well as provide help and support to get your business back on track.
You can also find out more about digital security risks by exploring our cyber insurance hub which includes helpful guides:
Need help with your insurance?
Whether you need a quote, have a general enquiry, or want to talk it through over the phone, we're here to help.
Make an enquiry – general and locations
Related guides and insights

Cyber security audits explained
Cybercrime is one of the biggest threats to businesses across all industries and having appropriate cyber security in place is vital. We take a look at cyber security audits, how they work and why they're important.
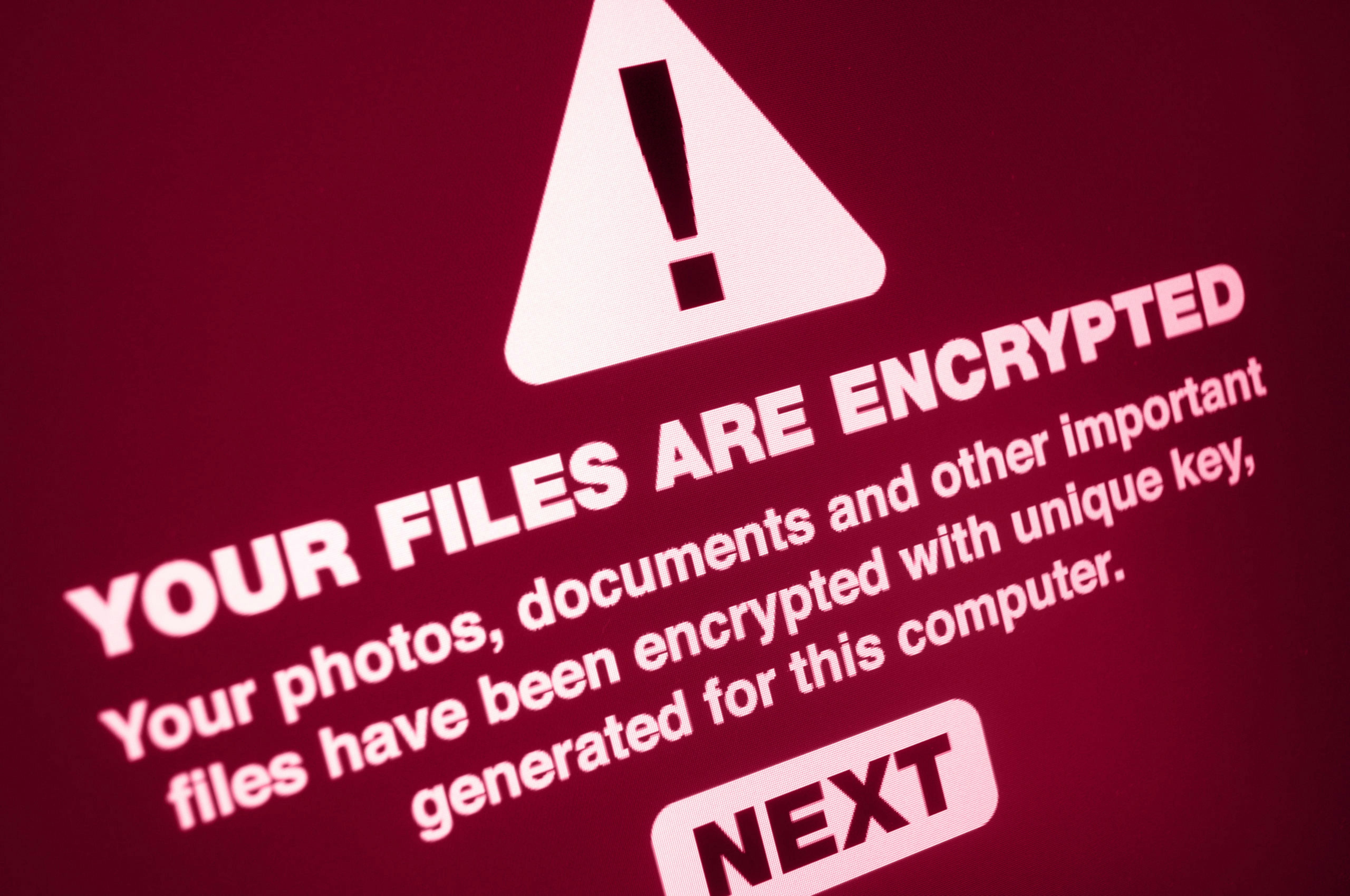
What is ransomware?
It’s crucial to understand the different types of malicious software so that you can ensure your systems are secure.

GDPR & Cyber insurance
Everybody in the business world is talking about GDPR at the moment. However, we should not overlook the wider business considerations which sit within appropriate data management and the risks and liabilities these present.
