What is a phishing attack?
Cybercrime costs the UK economy an estimated £14.7 billion a year, with phishing the most common type of attack.
29.04.26
By
![]() Phil Thorpe
Phil Thorpe

In this article
Unfortunately, as criminals and technology become more sophisticated, scams can be harder to detect. Recently, the rise of AI-powered phishing has made attacks more convincing than ever. To help you stay one step ahead, here’s what you should know about phishing and how you can keep your business safe.
What is phishing?
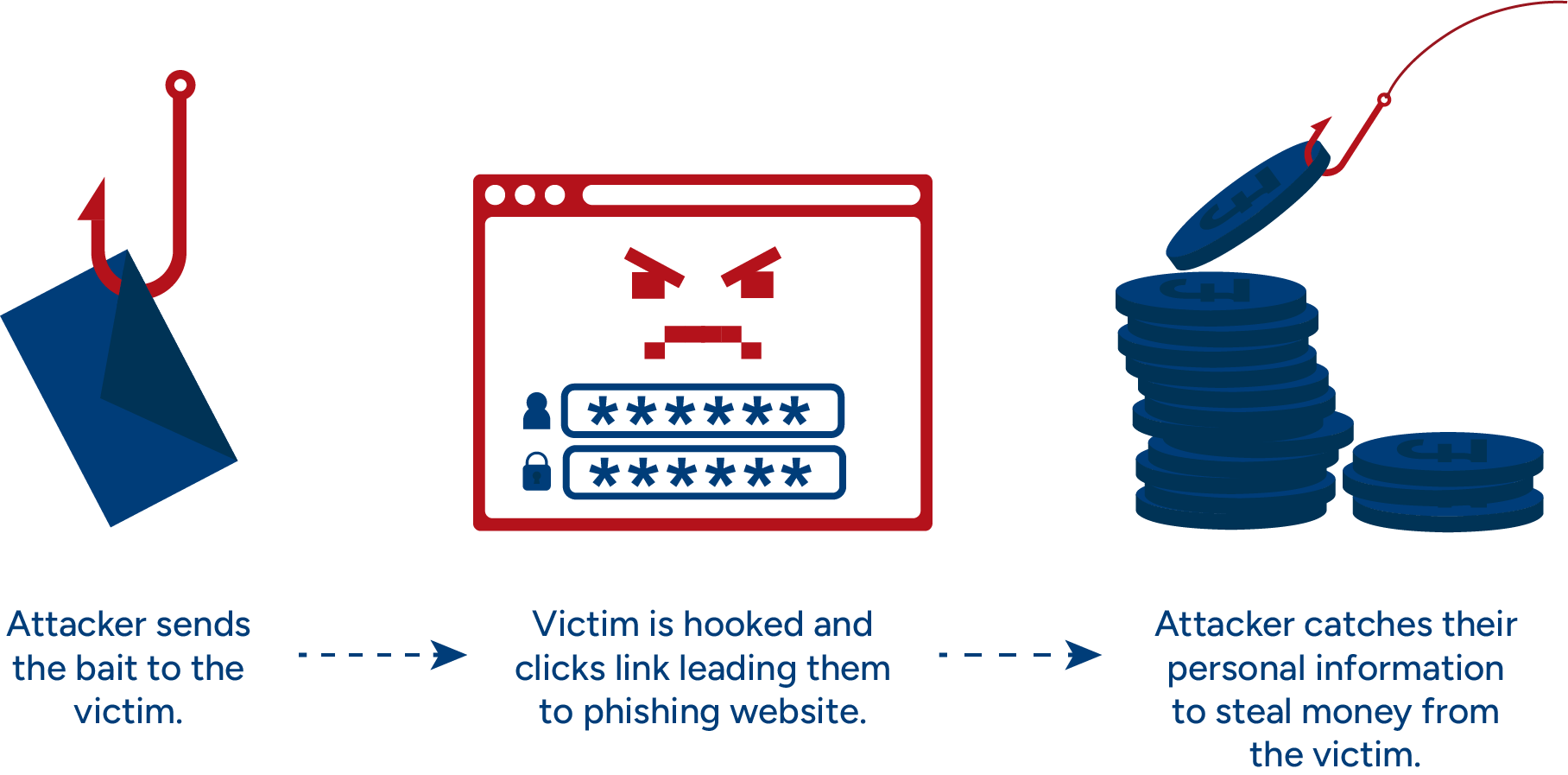
Phishing is a way of getting you to disclose personal information that can be used to steal money from you. Criminals will do this by masquerading as a legitimate business or organisation using fake emails or websites.
The technique is also a way to infiltrate your computer network to install malware (malicious software) that can corrupt your data. Again, the end goal is to extort money, and criminals will ask you to pay a ransom to decrypt your files.
Phishing is one of the oldest types of cybercrime, dating back to the 1990s. The very fact that it’s been around so long highlights how effective it is at helping criminals get what they want.
Why is it called phishing and not fishing?
Phishing is a technique that ‘baits’ users, and this is where the fishing analogy comes from. The use of ‘phishing’ instead of just ‘fishing’ is rumoured to be a nod back to an even older type of scam called phone phreaking.
Types of phishing attacks
Fundamentally, phishing is about tricking you into willingly giving up sensitive information through deception, including usernames, passwords, and credit card and bank details.
In most phishing cases, criminals send their victims some form of communication. This is usually an email, but it could be a text message or even via a website. These days, more of these communications are generated by AI, making them harder to detect.
It’s important not to underestimate just how convincing phishing attacks can be. It’s a method so well evolved that phishing is now an umbrella term for a range of specific attacks. Types of phishing include:
Email phishing
This is the simplest type of deception. A criminal will pose as a genuine client, business, or organisation. In many cases, they’ll send a simple message asking you to log in to your account or make a payment.
Email phishing is typically carried out on a blanket scale, targeting thousands of people at once in the hope that a handful will be duped.
Spear phishing
This is very similar to email phishing, but in these cases, a specific person is targeted. Criminals may also already have information about the person they target, which can make emails appear even more convincing.
Whaling
Another targeted form of phishing, this time aimed at management. As this is directed at senior executives, the deception is often far more sophisticated and can be very subtle.
Criminals carrying out whaling scams tend to focus on sending fake emails from government agencies, such as HMRC.
Angler phishing
This centres on social media and deceiving victims through fake posts and direct messages. When users click on links, they unwittingly download malware, giving criminals access to their social media accounts.
Fake websites
Criminals send phishing emails with links to fake or dummy websites that appear to be the real one. These can be very convincing, and criminals can even buy packages known as exploit kits to make their deceptions appear genuine.
Smishing and vishing
Smishing is duping victims using their mobile phones, for example, through text messages or in-app purchases. Vishing is similar but uses voicemail rather than text.
A common theme in all phishing examples is urgency. Criminals will try to convince you that action needs to be taken immediately by suggesting your account has been suspended or hacked. They may also say that you owe money to HMRC or haven’t paid vehicle excise duty (car tax), for example.
What is AI phishing?
With the proliferation of artificial intelligence, it’s worth shining a spotlight on the growing threat of AI phishing. In essence, criminals use AI to make phishing attacks more convincing and harder to detect. While traditional phishing relied on volume (sending the same generic message to thousands of recipients and hoping a few would be fooled), AI allows criminals to automate personalisation at scale. This allows them to craft large numbers of targeted messages that feel far more credible to the individuals receiving them.
AI tools can also analyse publicly available information about a target, from LinkedIn profiles to company websites, and use it to generate messages that mimic the tone and style of legitimate correspondence. The result is a new generation of phishing attacks that are faster to produce, harder to detect, and increasingly difficult to filter using conventional security software.
What is an example of AI phishing?
One of the clearest examples of AI phishing is the use of large language models (LLMs) to eliminate the signs that have traditionally helped people identify scams. Spelling mistakes, awkward grammar, and stilted phrasing have long been red flags, but AI can now produce fluent, natural-sounding English (or other languages). This helps to ensure that messages are plausibly from a real colleague, supplier, or institution.
One common AI phishing technique involves a criminal impersonating a senior member of staff. They will send a convincing email to someone in the finance department, requesting an urgent payment to a particular business. Because AI can tailor the message with real details about the business, names, job titles, and recent projects, it can be extremely difficult to tell apart from a genuine internal communication. For this reason, you should always check whether the bank details in any request or on any invoice belong to the intended recipient.
AI is also being used to power voice phishing (vishing), where criminals clone the voice of a trusted person using audio samples gathered online. In one documented case recorded by the National Crime Agency, a finance worker was deceived into transferring £20 million after attending what appeared to be a legitimate online meeting with company colleagues; every participant on the call had been deepfaked using AI.
How serious is phishing?
Phishing might be an older scamming method, but it’s effective and evolving all the time and AI has made this activity much easier and quicker to produce. The most recent government data reveals that:
Phishing is the most common type of cyberattack, affecting 85% of UK businesses that reported a breach or attack in the past year.
43% of UK businesses experienced a cyber breach or attack in the last 12 months.
Organisations are increasingly aware that AI-enhanced phishing methods are becoming mainstream, according to qualitative findings in the same survey.
How to prevent phishing attacks
Because AI-generated phishing removes many of the textual clues people have traditionally relied on to identify a scam, preventing it requires adopting a more thorough approach. The following steps can help protect your business from AI phishing attempts:
Don’t rely solely on grammar and spelling checks. AI-generated phishing emails are often grammatically correct, so an email that reads well is no longer a guarantee of legitimacy. Apply the same level of scrutiny to well-written messages as you would to any other.
Verify unexpected requests through a second channel. If you receive an unusual request by email, particularly one involving payments, credentials, or sensitive data, confirm it by phone or in person using the contact details you already have. Do not reply to the email itself or use any number provided within it.
Don’t forget the ‘don’t panic’ principle. Because AI messages are usually more convincing, the pressure to act immediately can feel more legitimate. Pause, question the request, and take the time to properly check it – a genuine colleague or supplier will understand a brief delay. If your firm has IT resources (whether internally or outsourced), check any suspicious activity with them before acting.
Update your staff training to cover AI-enabled threats. Awareness is still the best defence, but training needs to reflect how phishing has evolved. Staff should understand that a convincing, personalised, and error-free email is no longer evidence of authenticity, and that AI voice cloning is an emerging tactic used alongside email-based attacks. You may want to consider using a specialist cyber consultant who will be able to highlight and guide you through this process.
Can cyber insurance protect businesses?
Policies can’t protect you from becoming a victim of a cyberattack, but they can help you manage the consequences, including cover for extortion and fraud. Policies can also compensate you for business interruption and data loss.
At Alan Boswell Group, we also understand that the type of cyber insurance policy that’s right for you will depend on the nature of your business.
Need help with your insurance?
To find out more about how we can help you and your business, head to our cyber insurance hub. Alternatively, you can speak to an expert member of our team for bespoke advice.
Related guides and insights
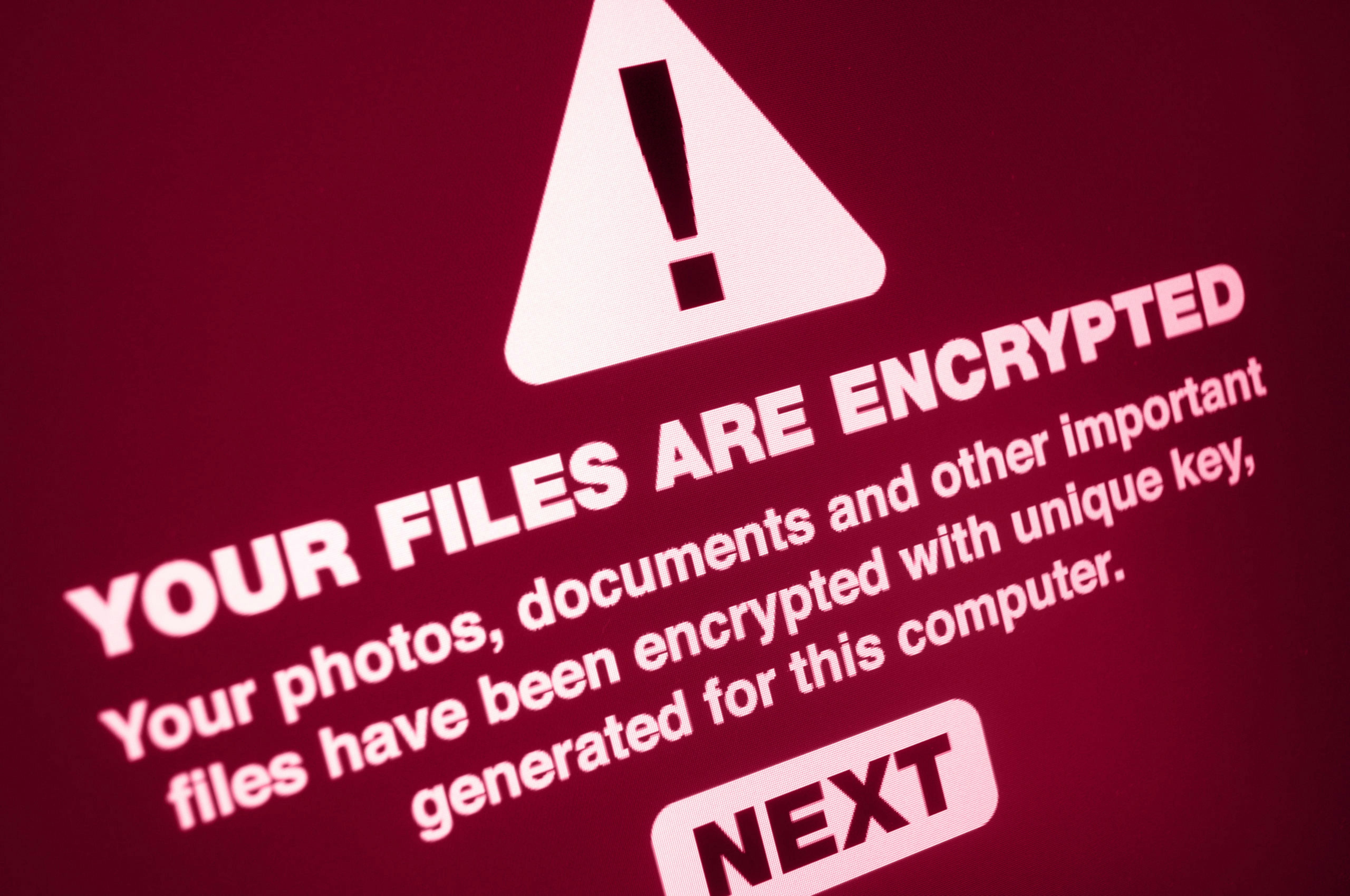
What is ransomware?
Ransomware is a type of malicious software that stops you from accessing your computer systems. We look at how it works, how to prevent it, and what to do if you’re unfortunate enough to experience an attack.

What is a cyber incident response plan?
A cyber incident response plan (IRP) outlines your business’s approach to handling a cyber security incident. Here’s why all businesses should have a plan to protect against the threat of cyber attacks.

Data protection insurance – protecting your business from data breach risks
For businesses that fail to protect personal or sensitive data, the financial penalties can be crippling. We look at how data protection insurance can help minimise financial and reputational damage.

Cyber security audits explained
Cyber security audits help identify weaknesses and vulnerabilities, thereby lowering the risk of your business becoming a victim of cybercrime.
